Rclone Ftp 553 Users May Not Upload Files
Transferring leverage in a ransomware attack
Defenders tin can sabotage double extortion ransomware schemes by detecting unusual file transfer utilities such as Mega and Rclone.
Ransomware has e'er been virtually leverage, and sometimes, just encrypting files is enough to get a payment. However, as organizations have gotten better about information backup and recovery practices—by implementing policies like the "3-ii-1 rule," for example—ransomware operators find themselves having to use more and unlike kinds of leverage.
A so-called "double extortion" scheme, where an adversary encrypts files and threatens to leak stolen data, is one prominent example of this. In fact, the extortion side of these schemes is proving and so constructive that one prominent ransomware group recently announced that it would stop encrypting files and focus entirely on extortion moving forward.
While piling extortion on top of ransomware is an effective style of increasing leverage, it also adds conspicuous opportunities for detection in the class of illicit file transfer activity. This post offers some detection strategies that security teams tin can employ to detect malicious file transfer action. Since we're publishing this on Star Wars Day, nosotros'd like to take you on an epic detection adventure. May the fourth exist with you lot!
With the growing number of data fill-in solutions, it tin exist difficult to decipher where ransomware operators might choose to store their newly stolen data. Detection can be a particular claiming when adversaries cull to utilize services that are common in enterprise environments, like Google Drive or Amazon S3. Luckily for us though, they very frequently use cloud storage services that aren't normal in enterprise environments. And even when adversaries exfiltrate your data to seemingly normal cloud storage providers, they often do so with unusual file transfer utilities.
Reddish Canary has observed Mega.io used as an exfiltration destination in multiple incident response engagements this twelvemonth. In these attacks, we've also witnessed adversaries leveraging legitimate file transfer utilities that Mega provides for gratuitous to its customers, making it easy for users to upload files. We've identified exfiltration to file sharing services via other tools as well, merely we're going to focus entirely on Mega-related tools, like MegaSync and MegaCmd, and on the open up source, cantankerous-platform utility Rclone.
Asking the correct questions
Even if our focus is somewhat express, the detection principles included in this commodity tin can be readily bathetic and applied to additional file transfer utilities and other legitimate tools that are existence co-opted for evil. But alerting on the use of whatsoever of these tools is petty, and we include various binary metadata below that y'all tin employ to accomplish simply that. Unfortunately, our experience across many short term incident response engagements is that adversaries generally endeavour to evade simple security controls past renaming these tools.
As such, you lot'll need to empathize the following:
- The authorized file sharing services and utilities in your environment
- The file sharing services and tools used in your environment, authorized or not
- The normal installation file paths for these tools
- The legitimate binary metadata associated with these tools
- The behaviors typically associated with these tools, including if and where they make network connections
Mega detection
Mega provides users with finish-to-end encryption of files, a gratis basic storage tier, and a suite of tools used to transfer files remotely. Rather than hassling with hosting their own file sharing servers, adversaries would rather make utilize of already existing cloud storage, especially ones that allow semi-anonymous payment via cryptocurrency similar Bitcoin. Simply blocking network connections to Mega-related IP addresses might be a viable security command in certain environments, but detecting the actual file transfer utilities that adversaries leverage volition offer improve defense-in-depth against illicit data transfer.
1 such utility is Mega'south main client application MegaSync, which is designed for routine file transfers and operates similarly to other cloud storage software such as Google Drive and Dropbox. In addition to MegaSync, we've besides observed adversaries using the interactive command line variant known as MegaCmd. This tool offers many of the same capabilities as MegaSync just from the command line.

Establishing the baseline
Under normal circumstances, you lot tin can await MegaSync to accept the following attributes:
| Metadata attribute | Value |
|---|---|
| Metadata aspect : Process name | Value : |
| Metadata attribute : Procedure path | Value : |
| Metadata attribute : Description | Value : MEGAsync |
| Metadata attribute : Internal proper noun | Value : |
| Metadata attribute : Product name | Value : MEGAsync |
It'southward important to empathize these baseline attributes considering adversaries rarely execute tools like MegaCmd or MegaSync under their original filename. In this style, successful detection requires that you are able to decide the true identity of a given procedure regardless of what it claims to be. In other words, you might achieve a expert detection issue by identifying processes based on metadata like their internal proper noun then alerting when the internal name and the presented process name do non match. Similarly, you may be able to accomplish success by looking for file path deviations.
Overt utilize of Mega
Adversaries oftentimes rename MegaSync to circumvent application controls in environments where the utility is not approved for use. Notwithstanding, this isn't always the case. Trend Micro has reported that the Nefilim ransomware only drops MegaSync into its normal file path nether its normal proper noun. If MegaSync isn't approved software in your environment, and so y'all may be able to detect its utilise by looking for the execution of a procedure that is megasync.exe from a path that includes the following: \\AppData\\Local\\MEGAsync
On acme of client applications such as those provided past Mega, many ransomware families may apply other software or born operating system utilities to exfiltrate data. We'll use Mega as the example here, merely you could just also replace mega.io with whatsoever service you want to look out for. Since blocking a domain outright is fiddling, we'll assume that y'all're okay with web browsers making network connections to Mega but want to know when annihilation else does.
If that's the instance, you tin look for execution of any process that is notchrome.exe,firefox.exe, safari.exe, opera.exe, iexplore.exe, microsoftedge.exe, microsoftedgecp.exe, browser_broker.exe, msedge.exe, or dauntless.exe initiating a network connectedness to the domains mega.io or mega.co.nz.
Abnormal installation paths
In some instances, adversaries will execute MegaSync under its existent proper name just from an unusual installation path. A detection analytic for identifying relocated copies of MegaSync execution may look something like this:
- Binary named
megasync.exe - File execution path does not include
AppData\\Local\\MEGAsync\\
If there are circumstances in which it'southward adequate for Megasync to run from an abnormal directory, and then consider tuning your detection logic accordingly.
Renaming MegaSync
Nosotros've observed adversaries executing renamed instances of Mega during incident response engagements associated with ransomware families like Nefilim, Sodinokibi, Pysa, and Conti. Alerting on the use of renamed instances of MegaSync could help prevent or reduce the scope of like incidents moving forward. The following pseudo-analytic should detect renamed instances of MegaSync:
- Await for the execution of a process that is not named
megasync.exebut that executes with any any of the following respective metadata:- a binary internal name that is
megasync.exe - a binary product proper noun that is
MEGAsync - a binary description that is
MEGAsync
- a binary internal name that is
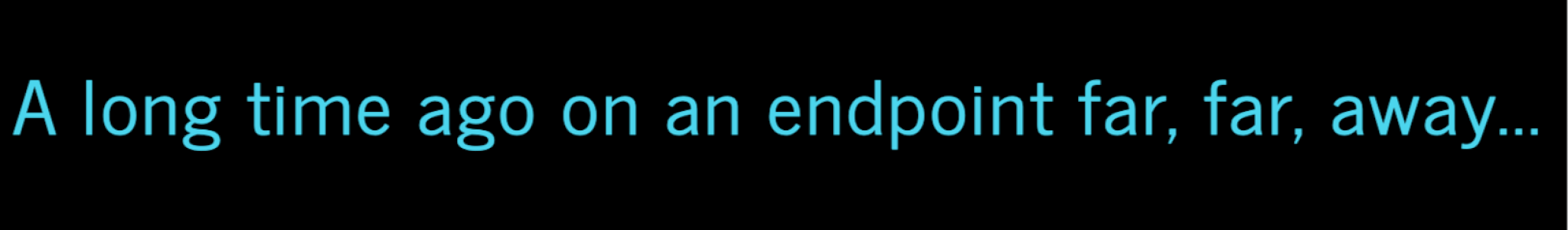
The following epitome shows the execution of meg.exe. However, examining binary metadata reveals that meg.exe was in fact a renamed instance of MegaSync.
Rclone detection
Shifting our focus away from Mega-specific tooling, it wouldn't be a blog post about exfiltration if we didn't smoothen a lite on the cross-platform, open source file transfer utility known as Rclone. Once a ransomware operator has hooked an organization, Rclone helps them reel in their catch. Without the power to cut the data loose, whatsoever attempts at double extortion go out the window.

And so, what makes Rclone so special? Its versatility. In one case an adversary drops information technology on an endpoint, modifying the exfiltration destination is trivial. Adversaries tin also cull from a listing of born command flags that will perform various actions, or they tin can opt to supply their own configuration file and avoid the need to execute with various command line flags. As an example, mayhap using a cloud storage provider is non an choice considering of a technical command that disallows network connections to the antagonist'south hosting provider of choice. Rclone makes information technology very simple to use file transfer protocols such every bit FTP or SFTP, finer enabling adversaries to motion files wherever they want. See the Appendix for a listing of known and supported Rclone commands at the end of this report.
Establishing the baseline
As was the example with MegaSync, understanding the binary metadata associated with Rclone is a necessary first step if you desire to discover adversaries who rename the tool. Under normal circumstances, you can wait rclone to have the post-obit attributes:
| Metadata attribute | Value |
|---|---|
| Metadata attribute : Process proper noun | Value : |
| Metadata attribute : Original name | Value : |
| Metadata attribute : Clarification | Value : Rsync for cloud storage |
| Metadata attribute : Internal name | Value : |
| Metadata attribute : Company proper name | Value : |
| Metadata attribute : Product name | Value : Rclone |
Overt use of Rclone
If Rclone isn't permitted in your surround, then you tin can simply look for the execution of a process named rclone.exe. It's worth noting that there isn't whatever standard path that Rclone executes from, so unfortunately nosotros cannot pare things downward further like nosotros were able to with MegaSync.
Renaming Rclone
Red Canary has observed the execution of renamed versions of Rclone during IR engagements, in an attempt to bypass basic application controls. Taking this into business relationship, we can begin creating detection analytics for renamed instances of Rclone, just as we did with MegaSync.
Yous can do so past looking for the execution of a process that is non named rclone.exe but that executes with any of the following binary metadata:
- a binary original proper noun that is
rclone.exe - a binary description that is "Rsync for cloud storage"
- a binary internal name that is
rclone - a binary company name that is
https://rclone.org - a binary product name that is
Rclone
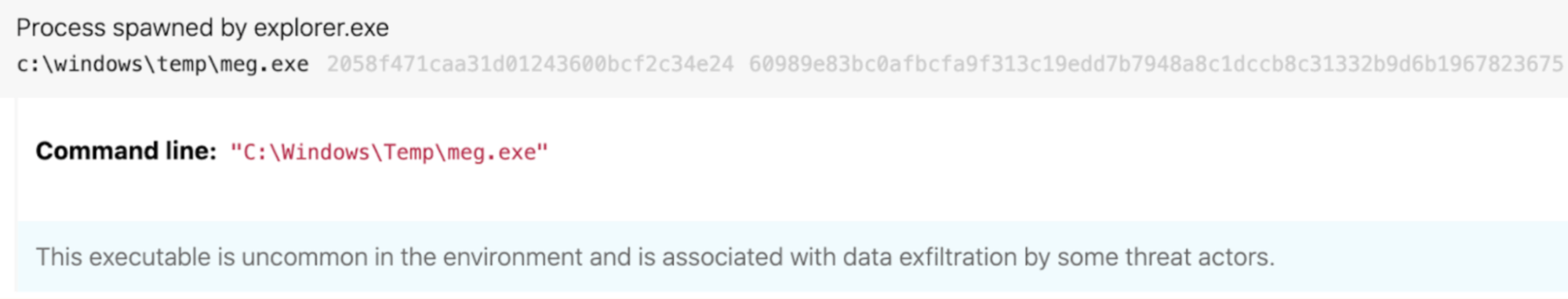
The following epitome shows the execution of sihosts.exe. Even so, an exam of binary metadata revealed that sihosts.exe was in fact a renamed example of Rclone:
Suspicious command line flags
In the interest of building resilient detection analytics, it's worth noting that metadata could be altered in some way for these binaries, enabling an adversary to circumvent some of the security controls mentioned higher up. Considering that, information technology'due south worth looking out for command line flags that are consistent with suspicious executions of rclone as well (run into Appendix for the list of helpful control line perimeters).
Any time you observe these control line flags in play, it might exist time to get your magnifying lens out and dig into how Rclone is existence used in your environs. Of course, this can differ from i system to the next. If you have approved legitimate apply cases for Rclone in your surround, and then you may have to tune your analytics appropriately.
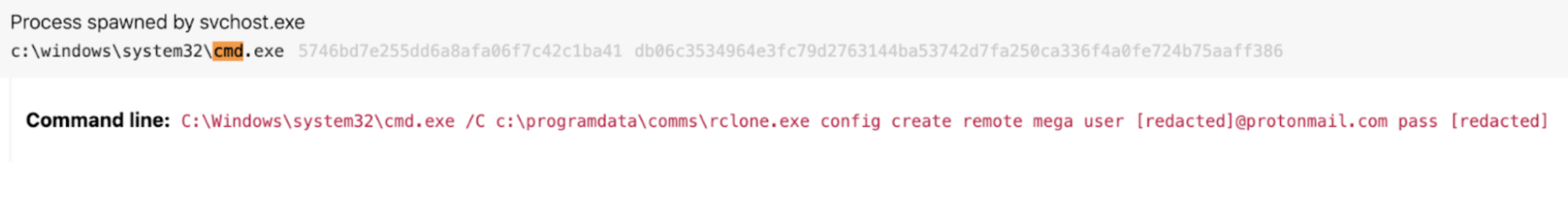
Nosotros've had success looking for control lines including one or more of the control line parameters: rclone, lsd, remote:, ftp:, mega, --config, --machine-confirm, or--multi-thread-streams and copy, config, create, lsd, remote, mega, user, pass, --config, --progress, --no-check-certificate, --ignore-existing, --auto-confirm, --multi-thread-streams`, --transfers, ftp:, remote:, or \\.
The following image shows what some of these command line flags might expect like in the wild:
While this is a great identify to start, the Rclone project is constantly being updated with new functionality, and then keeping an eye on the ChangeLog and Docs may be helpful when looking for new ways to identify the utility moving frontward.
Recall: detect or do not discover. There is no endeavour.
Appendix
Every bit promised, the following tabular array includes a list of Rclone commands that may be of particular involvement.
| Flag | Activeness |
|---|---|
| Flag: | Activeness : Sync files to a destination |
| Flag: | Action : Copy files to a destination |
| Flag: | Action : Specify a configuration file |
| Flag: | Action : Create a configuration file |
| Flag: | Activity : List directories |
| Flag: | Action : Defines a remote destination when edifice a configuration file |
| Flag: | Action : Mega, the deject provider, divers while building a configuration file |
| Flag: | Action : Username to authenticate to a remote destination |
| Flag: | Action : Password to authenticate to a remote destination |
| Flag: | Action : Specifies a configuration file to use in lieu of direct CLI commands |
| Flag: | Action : Lists the progress of files being transferred |
| Flag: | Action : Skips certificate checks when brokering a network connection |
| Flag: | Action : Ignores any files that may already be on a remote destination |
| Flag: | Action : Yeah to all confirmation prompts |
| Flag: | Activeness : Define the maximum number of streams for transferring files |
| Flag: | Action : Defines the maximum number of concurrent transfers |
| Flag: | Activeness : A predefined FTP destination, observed in straight CLI execution |
| Flag: | Action : A predefined remote destination, observed in directly CLI execution |
| Flag: | Activity : Not a flag, but a CLI option consistent with network shares |
Related Articles
Better know a data source: Access tokens (and why they're hard to get)
Unwrapping the 2022 Threat Detection Written report
Intelligence Insights: March 2022
Uncompromised: When REvil comes knocking
Subscribe to our blog
Our website uses cookies to provide yous with a meliorate browsing experience. More than information can be institute in our Privacy Policy.
X
Source: https://redcanary.com/blog/rclone-mega-extortion/

Post a Comment for "Rclone Ftp 553 Users May Not Upload Files"